Ghostscript Security Vulnerability
On August 21, 2018, several Ghostscript security vulnerabilities with were found by a Google Project Zero security researcher. These vulnerabilities could allow a remote, unauthenticated attacker to execute arbitrary commands if a specially crafted PDF or PS (Postscript) file is processed.
Many of our Document Conversion Service clients use GhostScript to convert PDF documents. In light of this vulnerability, we wanted to address this issue as it relates to Document Conversion Service, and explain how our clients can protect themselves.
With the release of Ghostscript 9.24 on September 3, 2018, Artifex Software has stated that all found issues have been resolved. We have completed our integration testing of this version with Document Conversion Service and recommend installing GhostScript 9.24 or later as soon as possible.
Note: Before updating GhostScript, or uninstalling the older versions, we recommend stopping your Document Conversion Service if it is running. Make the necessary changes and then restart and test that your conversion service is running as expected.
How Can I Tell if I am Using GhostScript?
By default the DCS configuration uses Adobe Reader for PDF conversion. In most cases, the DCS configuration will have been modified to disable PDF conversion using Adobe Reader; this causes DCS to use GhostScript to convert PDF files.


If you are running DCS 3.0.014 or later, and have not modified the DCS configuration file to use a particular Ghostscript version, DCS will automatically detect and use the most recent Ghostscript version.
How Do I Set the Ghostscript Version?
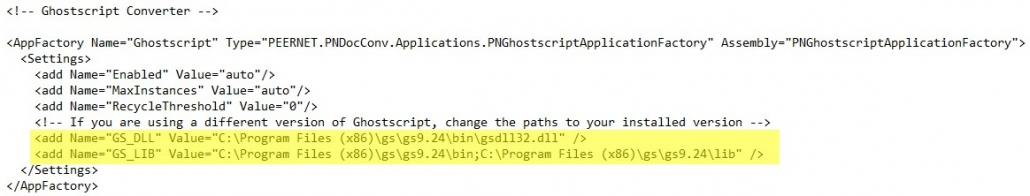
For anyone using a version of DCS prior to 3.0.014, or if you have edited the configuration file to use a particular Ghostscript version, you will need to update your DCS configuration file to use the correct version of Ghostscript:
If you have any further questions or concerns about GhostScript, please do not hesitate to contact our support team.
Related Links:
https://www.kb.cert.org/vuls/id/332928